March 23, 2021
No Criminal Is an Island

Laura O'Driscoll
Content Manager
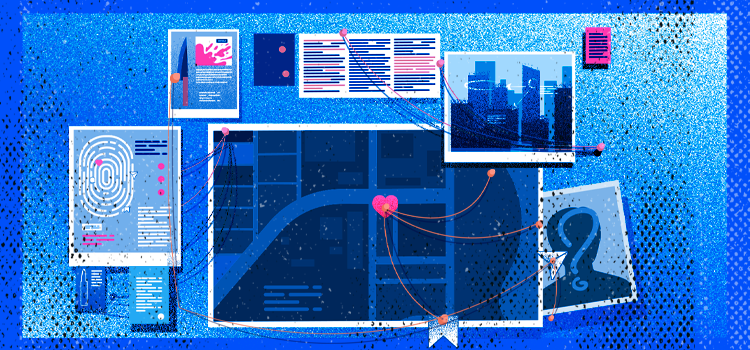
From ISIS to Q-Anon, criminal networks, and financial frauds: large-scale violence and crime are rarely the work of isolated individuals. “Networked actors” like these are increasingly notorious for their widespread use of social media to communicate, recruit, disseminate ideology, and plan violent or criminal action. But their Twitter proficiency is a double-edged sword. The reams of data produced by social media interactions can be utilized by opponents to map the network and understand how it functions. This data can even be instrumentalized against them, to counter-narratives and neutralize activities.
This process - known as social network analysis - existed long before the dawn of social media. It is a discipline that charts the interactions between people, places, and things, to understand the larger framework and context within which they operate. At its most effective, where human insight is combined with powerful open source intelligence (OSINT) technology, it is a tool for prediction, prevention, and intervention when it is most needed.
Social Animals: How Networks Think
Social network analysis works on the principle that beneath every large structure is a complex ecosystem made up of individual parts, which together allow it to function as a whole. This structural environment is made up of links (relationships and patterns) between individual actors and entities (nodes).
Nodes are inherently interdependent. They allow the overall network to function, and the network in turn gives them a function. Links are enduring yet dynamic. They represent not just connections but exchanges, and channels for the flow of resources or information. This structural environment allows you to see and understand the bigger picture beyond individual actors, and how interactions generate action. That means understanding not just what is happening, but why, where, how, and through whom. At its most effective, it means using that understanding to forecast what may happen in the future and weaponizing it to design and implement counter-campaigns.
Written in the Stars: The Social Media Effect
The dawn of social media has generated an ever-increasing wealth of data points through which to analyze networked actors. Usernames or “handles” frame public interactions between users. Keywords or “hashtags” chart the flow of information and resources and connect conversations across diverse platforms and geographies. Lists of “friends” and “followers” combine with “likes”, “comments”, “mentions”, “tags”, “shares” or “retweets”, “threads” and “replies” to create a constellation of usable data.
But skilled analysis isn’t as simple as just joining the dots to see who is connected to whom. A nuanced understanding of the larger network means analyzing the quality, quantity, and nature of interactions; the direction of travel of information, and the context in which its meaning involves and changes; and the relative involvement and importance of individual nodes in this process. If the links and nodes make up the skeleton, the analysis puts flesh on the bones. It looks to understand and predict how the body thinks and moves as a whole.
Countering Violent Extremism Online
The effort to counter violent extremist ideology is a prime case for the real-world application of social network analysis. Groups like ISIS and QAnon are essentially networks composed of multiple individual actors, socially connected, and united behind certain goals and narratives. As the development and dissemination of group ideology often play out online, social network analysis can be used to see how key “influencers” exploit social media. Once understood, their own techniques can be used against them.
ISIS, for example, has notoriously leaned on social media both to propagate ideology and for recruitment purposes. The data generated by their prolific Twitter usage can be used to map out actors and influencers, and to understand their core communication frameworks (including keywords, narratives, and shared language). Analysts can pinpoint how and where the network engages fruitfully with new and existing followers. As demonstrated in research by RAND, this can be used to create a blueprint from which to conduct counter-messaging campaigns, using the network’s own structural dynamics against them.
Far-right hate groups, meanwhile, are renowned for their love of fringe forums like Gab, Parler, MeWe, 4chan, and 8kun, often assuming that such forums increase anonymity. In fact, this assumption can lead users to drop their guard and reveal more than they would on a mainstream forum. Users sharing hate speech, photographs, and video footage can unwittingly reveal identifying data including GPS coordinates, identifiable faces, and items or place markers that facilitate geolocation. Social network analysis that takes account of the vast spread of data across available platforms, however niche, will reap the benefits.
Beyond identification and counter-messaging, timely analysis can also facilitate intervention ahead of violent action. Following the storming of the Capitol in January 2021, analysts noted that the planning phase had taken place online and in plain sight. From the start of the new year, QAnon-linked accounts on Twitter alone were found to have posted more than 1,480 violent references to the 6th: yet observers were still surprised when extreme rhetoric tipped over into violent action. The more familiar an analyst is with a network’s “normal”, the better equipped they will be to spot abnormal developments in time to intervene.
Combating Financial Crime Online
Where social network analysis has a well-established record in countering extremist strategies, its use to detect and combat financial crime is slowly but surely gaining ground. Anti-money laundering protocols are at the spearpoint of this uptake. Traditionally siloed fraud detection methods are running up against increasingly capable fraudsters, whose relative agility makes it easy for them to evade standard risk-score-based analysis. This maneuverability comes from the fact that they usually do not act in isolation. Sophisticated fraudsters will either use or form part of, a larger network of actors and entities: exactly the kind of network that is ripe for social network analysis. Organizations with a handle on the dynamics and patterns of fraud, money laundering, terrorist financing, human trafficking, and organized criminal groups, will be better equipped to identify the agents of such networks when they come knocking.
What’s more, the recent GameStop scandal has flagged up another interesting use for social network analysis in the financial crime world. Over the last month, the United States Securities and Exchange Commission has reportedly been combing social media for signs that deliberate market manipulation online played a role in “talking up stocks”, leading to the unprecedented stock swings that rocked GameStop Corp and AMC Entertainment Holdings Inc, amongst others. They will be looking in particular for the deliberate planting and spread of misinformation across digital forums. Whilst not the first case of its kind, its outcome will be telling for the power of social media both to perpetrate and to counter, modern-day financial crime.
The Hybrid Approach: From Data to Bigger Picture
Social media is an unprecedented source of data: but this is only useful to analysts with the capability to collect it in the first place. The dizzying speed and volume at which online data is created, disseminated, changed, and deleted, makes comprehensive manual collection impossible for any but the smallest cases. This is where open source intelligence (OSINT) technology comes into its own.
When paired with tools that use advanced techniques such as machine learning and natural language processing, social network analysis is a powerful way to make sense of big data problems. The right technology can rapidly scour the full range of available online forums, accounting for different linguistic variations and nuances, and identify not just contemporaneous but archived sources, as well as unseen metadata. With large amounts of data collected efficiently and in a usable format, analysts will be in a position to make full and thorough use of it. A well-crafted hybrid approach, that uses the power of technology to gather data and the power of the human mind to interpret it, is the key to cracking the networks that perpetrate organized violence and crime.